Plano, Texas – March 29, 2022 – These latest enhancements allow customers to leverage Microsoft 365 Defender and MDR to not only identify but also immediately respond to breaches stemming from user account-based attacks. – Today, Critical Start, a leading provider of Managed Detection and Response (MDR) services, introduced industry unique capabilities around Managed Detection and Response (MDR) services for the Microsoft 365 Defender security suite that protect against phishing, brute force, and cloud application attacks on user credentials. Other MDR providers offer recommendations, while the Critical Start SOC responds on behalf of the customer to stop user account attacks that are often a precursor to a breach.
These enhanced capabilities allow customers to extend existing defenses and prevent breaches stemming from user account-based attacks. Figures and analysis from the 2021 Verizon Data Breach Investigations Report (DBIR) reveal that “credentials remain one of the most sought-after data types”, continuing a trend noted in previous iterations of the report. Since cyber-criminals are continuing to focus their attacks on credentials that will allow them to stay hidden as they access networks rather than hacking the networks themselves, users need to be able to quickly detect and easily take action to disrupt these attacks.
“By adding threat detection and response capabilities for credential and user account attacks into our MDR platform, Critical Start goes beyond the endpoint to protect against one of the most common attack vectors involved in the majority of breaches,” said Chris Carlson, vice president of product at Critical Start. “This new expansion of capabilities was developed in direct response from customers that MDR providers need to go beyond giving recommendations for action and swiftly respond to stop attacks in progress. Critical Start now grants our customers the ability to improve their organizations’ security postures as well as their overall readiness to face off against credential-based attacks.”
With the combined power of Critical Start’s existing MDR services and the Microsoft security suite, alerts can be brought in from multiple Microsoft systems, including user-reported email phishing attempts, Azure Active Directory identity alerts and alerts triggered by anonymous login IPs to business applications running from Defender for Cloud Apps.
The expanded offering allows for optimized detection and response for different kinds of attacks that could result in users’ account becoming compromised, including in the following use cases:
- Credential Harvesting through Email Phishing: Multiple steps in credential harvesting attacks, such as real phishing emails and malicious links, are detected. Critical Start provides courses of action to disrupt the chain and update potentially compromised user accounts.
- Attacks Against Cloud Applications: Adversaries that gain access to an organization’s cloud applications find themselves with access to the entire organization’s sensitive data. Critical Start’s Zero Trust Analytics Platform (ZTAP) automates investigating alerts from Microsoft 365 Defender suite products and elevates any real threats to the Critical Start SOC analysts for investigation. Critical Start can also provide responses for potentially stolen credentials including disabling an account, forcing a logout and enforcing password changes.
- Brute Force Attacks: When unable to gain access to an organization’s data through stolen or purchased credentials, adversaries will attempt to break in via brute force attacks with weak passwords. When this occurs, Critical Start’s platform automates investigating alerts from Microsoft 365 Defender suite products and elevates legitimate threats to the Critical Start SOC analysts for investigation. Critical Start can also provide responses for potentially stolen credentials including disabling an account, forcing a logout and enforcing password changes.
- Security Awareness Training to Defend against Phishing Attacks: Critical Start adds additional email phishing analysis in combination with Microsoft’s native capabilities, further supporting security awareness training by enabling a positive feedback loop informing employees of the outcome of the reported email.
More information can be found here: https://www.criticalstart.com/our-solutions/managed-detection-response-services/xdr/microsoft-365-defender/
About Critical Start
Today’s enterprise faces radical, ever-growing, and ever-sophisticated multi-vector cyber-attacks. Facing this situation is hard, but it doesn’t have to be. Critical Start simplifies the complexity of cybersecurity by extending your team with a comprehensive enterprise solution of flexible services, exclusive technology and seasoned security experts that deeply understand and adapt with your organization’s unique needs and collaborate with you to detect the right threats and respond with the right actions. We strive to provide peace of mind and value with contractual Service Level Agreements (SLAs) for Time to Detection (TTD) and Median Time to Resolution (MTTR) and 100% transparency into our service.
![]()
Transform Vulnerability Management: How Critical Start & Qualys Reduce Cyber Risk
In a recent webinar co-hosted by Qualys and Critical Start, experts from both organizations discusse...![]()
H2 2024 Cyber Threat Intelligence Report: Key Takeaways for Security Leaders
In a recent Critical Start webinar, cyber threat intelligence experts shared key findings from the H...![]()
Bridging the Cybersecurity Skills Gap with Critical Start’s MDR Expertise
During a recent webinar hosted by CyberEdge, Steven Rosenthal, Director of Product Management at Cri...![]()
2024: The Cybersecurity Year in Review
A CISO’s Perspective on the Evolving Threat Landscape and Strategic Response Introduction 2024 has...![]()
Modern MDR That Adapts to Your Needs: Tailored, Flexible Security for Today’s Threats
Every organization faces unique challenges in today’s dynamic threat landscape. Whether you’re m...![]()
Achieving Cyber Resilience with Integrated Threat Exposure Management
Welcome to the third and final installment of our three-part series Driving Cyber Resilience with Hu...Why Remote Containment and Active Response Are Non-Negotiables in MDR
You Don’t Have to Settle for MDR That Sucks Welcome to the second installment of our three-part bl...![]()
Choosing the Right MDR Solution: The Key to Peace of Mind and Operational Continuity
Imagine this: an attacker breaches your network, and while traditional defenses scramble to catch up...![]()
Redefining Cybersecurity Operations: How New Cyber Operations Risk & Response™ (CORR) platform Features Deliver Unmatched Efficiency and Risk Mitigation
The latest Cyber Operations Risk & Response™ (CORR) platform release introduces groundbreaking...![]()
The Rising Importance of Human Expertise in Cybersecurity
Welcome to Part 1 of our three-part series, Driving Cyber Resilience with Human-Driven MDR: Insights...![]()
Achieving True Protection with Complete Signal Coverage
Cybersecurity professionals know all too well that visibility into potential threats is no longer a ...![]()
Beyond Traditional MDR: Why Modern Organizations Need Advanced Threat Detection
You Don’t Have to Settle for MDR That Sucks Frustrated with the conventional security measures pro...The Power of Human-Driven Cybersecurity: Why Automation Alone Isn’t Enough
Cyber threats are increasingly sophisticated, and bad actors are attacking organizations with greate...Importance of SOC Signal Assurance in MDR Solutions
In the dynamic and increasingly complex field of cybersecurity, ensuring the efficiency and effectiv...The Hidden Risks: Unmonitored Assets and Their Impact on MDR Effectiveness
In the realm of cybersecurity, the effectiveness of Managed Detection and Response (MDR) services hi...![]()
The Need for Symbiotic Cybersecurity Strategies | Part 2: Integrating Proactive Security Intelligence into MDR
In Part 1 of this series, The Need for Symbiotic Cybersecurity Strategies, we explored the critical ...Finding the Right Candidate for Digital Forensics and Incident Response: What to Ask and Why During an Interview
So, you’re looking to add a digital forensics and incident response (DFIR) expert to your team. Gr...![]()
The Need for Symbiotic Cybersecurity Strategies | Part I
Since the 1980s, Detect and Respond cybersecurity solutions have evolved in response to emerging cyb...![]()
Critical Start H1 2024 Cyber Threat Intelligence Report
Critical Start is thrilled to announce the release of the Critical Start H1 2024 Cyber Threat Intell...![]()
Now Available! Critical Start Vulnerability Prioritization – Your Answer to Preemptive Cyber Defense.
Organizations understand that effective vulnerability management is critical to reducing their cyber...![]()
Recruiter phishing leads to more_eggs infection
With additional investigative and analytical contributions by Kevin Olson, Principal Security Analys...![]()
2024 Critical Start Cyber Risk Landscape Peer Report Now Available
We are excited to announce the release of the 2024 Critical Start Cyber Risk Landscape Peer Report, ...Critical Start Managed XDR Webinar — Increase Threat Protection, Reduce Risk, and Optimize Operational Costs
Did you miss our recent webinar, Stop Drowning in Logs: How Tailored Log Management and Premier Thre...Pulling the Unified Audit Log
During a Business Email Compromise (BEC) investigation, one of the most valuable logs is the Unified...![]()
Set Your Organization Up for Risk Reduction with the Critical Start Vulnerability Management Service
With cyber threats and vulnerabilities constantly evolving, it’s essential that organizations take...![]()
Announcing the Latest Cyber Threat Intelligence Report: Unveiling the New FakeBat Variant
Critical Start announces the release of its latest Cyber Threat Intelligence Report, focusing on a f...Cyber Risk Registers, Risk Dashboards, and Risk Lifecycle Management for Improved Risk Reduction
Just one of the daunting tasks Chief Information Security Officers (CISOs) face is identifying, trac...![]()
Beyond SIEM: Elevate Your Threat Protection with a Seamless User Experience
Unraveling Cybersecurity Challenges In our recent webinar, Beyond SIEM: Elevating Threat Prote...![]()
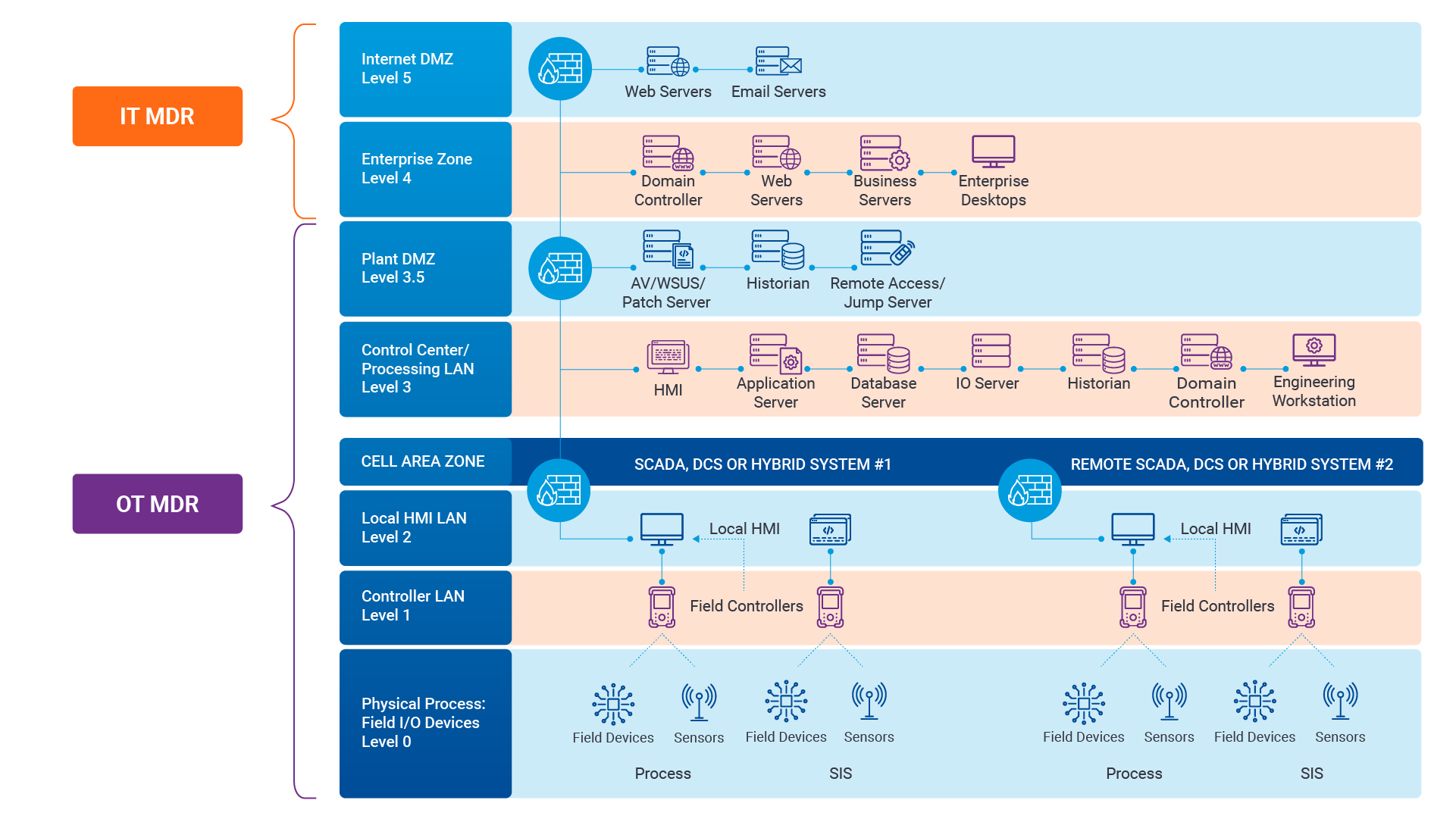
Navigating the Convergence of IT and OT Security to Monitor and Prevent Cyberattacks in Industrial Environments
The blog Mitigating Industry 4.0 Cyber Risks discussed how the continual digitization of the manufac...![]()
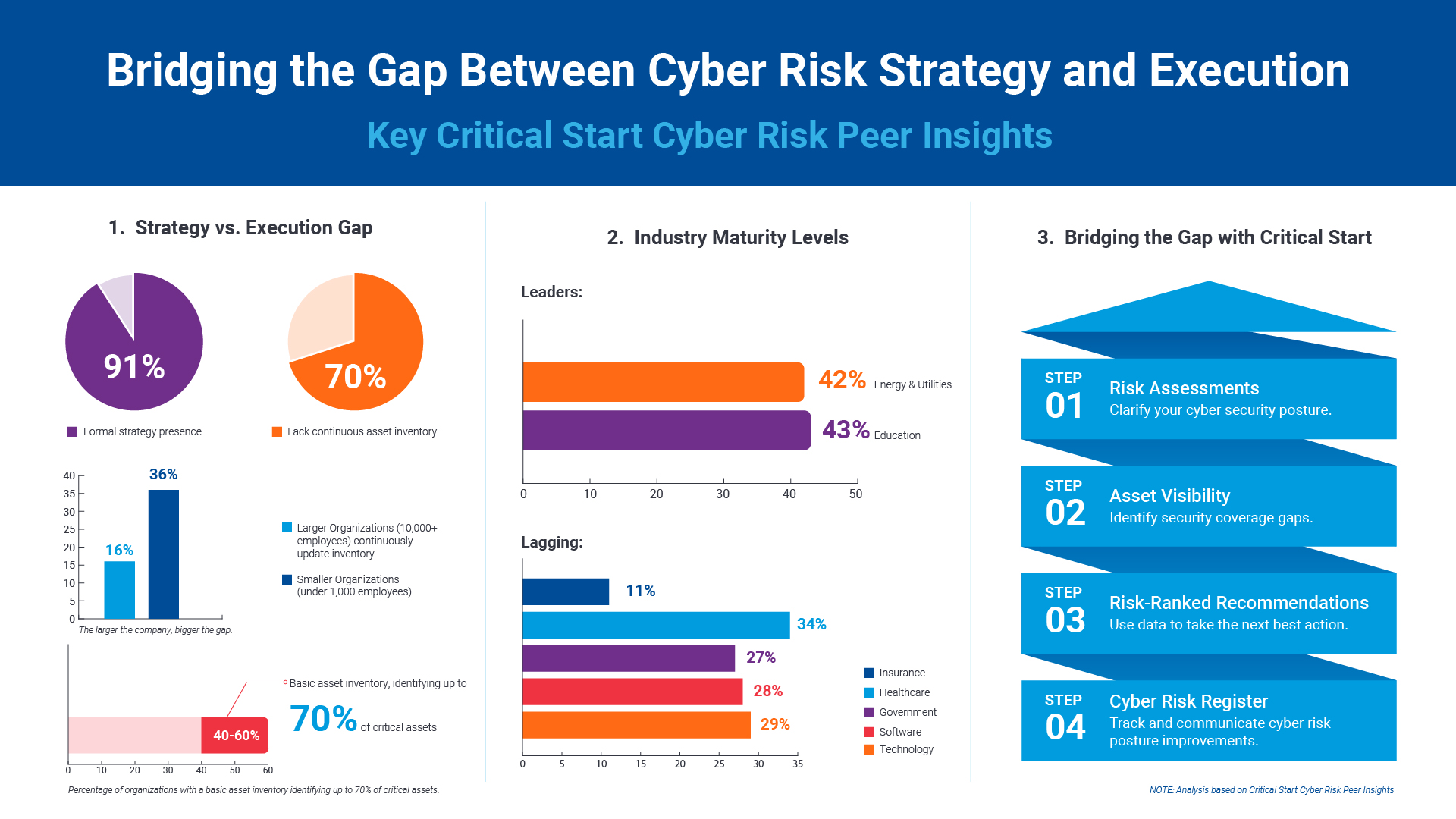
Critical Start Cyber Risk Peer Insights – Strategy vs. Execution
Effective cyber risk management is more crucial than ever for organizations across all industries. C...![]() Press Release
Press ReleaseCritical Start Named a Major Player in IDC MarketScape for Emerging Managed Detection and Response Services 2024
Critical Start is proud to be recognized as a Major Player in the IDC MarketScape: Worldwide Emergin...Introducing Free Quick Start Cyber Risk Assessments with Peer Benchmark Data
We asked industry leaders to name some of their biggest struggles around cyber risk, and they answer...Efficient Incident Response: Extracting and Analyzing Veeam .vbk Files for Forensic Analysis
Introduction Incident response requires a forensic analysis of available evidence from hosts and oth...![]()
Mitigating Industry 4.0 Cyber Risks
As the manufacturing industry progresses through the stages of the Fourth Industrial Revolution, fro...![]()
CISO Perspective with George Jones: Building a Resilient Vulnerability Management Program
In the evolving landscape of cybersecurity, the significance of vulnerability management cannot be o...![]()
Navigating the Cyber World: Understanding Risks, Vulnerabilities, and Threats
Cyber risks, cyber threats, and cyber vulnerabilities are closely related concepts, but each plays a...The Next Evolution in Cybersecurity — Combining Proactive and Reactive Controls for Superior Risk Management
Evolve Your Cybersecurity Program to a balanced approach that prioritizes both Reactive and Proactiv...![]()
CISO Perspective with George Jones: The Top 10 Metrics for Evaluating Asset Visibility Programs
Organizations face a multitude of threats ranging from sophisticated cyberattacks to regulatory comp...![]()
Microsoft 365 Defender
24x7x365 threat detection and response with Managed Extended Detection and Response (MXDR) for Micro...![]()
Beyond the Endpoint: Detect and Disrupt User Account Attacks
By: Chris Carlson, VP of Product Management “What’s in a name?” For Shakespeare, it’s the st...
Newsletter Signup
Stay up-to-date on the latest resources and news from CRITICALSTART.
Thanks for signing up!